Showing 397–408 of 468 results
-
₹4,500.00
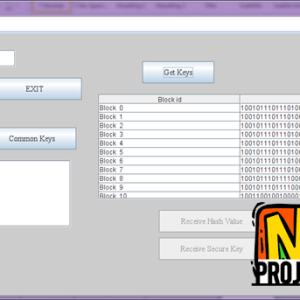
Securing Cloud Data under Key Exposure Abstract-Recent news reveal a powerful attacker which breaks data confidentiality by acquiring cryptographic keys, by means of coercion or backdoors in cryptographic software. Once the encryption key is exposed, the only viable measure to preserve data confidentiality is to limit the attacker?s access to the ciphertext. This may be…
-
₹5,500.00
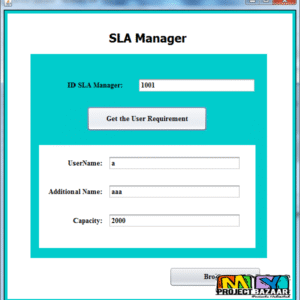
Securing Services in Networked Cloud Infrastructures Abstract?we propose techniques and architecture for securing services that are hosted in a multi-tenant networked cloud infrastructures. Our architecture is based on trusted virtual domains and takes into account both security policies of the tenant domains. < final year projects > [numbers_sections number=”1″ title=”Including =Packages=” last=”no” ] Complete Source…
-
₹4,500.00
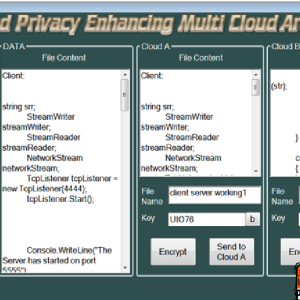
Security and Privacy Enhancing in Multi cloud Architecture Abstract? Security and Privacy Enhancing in Multi cloud Architecture Video View Demo [numbers_sections number=”1″ title=”Including =Packages=” last=”no” ] Complete Source Code Complete Documentation Complete Presentation Slides Flow Diagram Database File Screenshots Execution Procedure Readme File Addons Video Tutorials Supporting Softwares [/numbers_sections] [numbers_sections number=”2″ title=”Our =Specialization=” last=”no”…
-
₹4,500.00
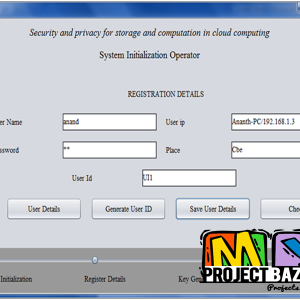
Security and privacy for storage and computation in cloud computing Abstract? Security and privacy for storage and computation in cloud computing. Video View Demo [numbers_sections number=”1″ title=”Including =Packages=” last=”no” ] Complete Source Code Complete Documentation Complete Presentation Slides Flow Diagram Database File Screenshots Execution Procedure Readme File Addons Video Tutorials Supporting Softwares [/numbers_sections] [numbers_sections…
-
₹4,500.00
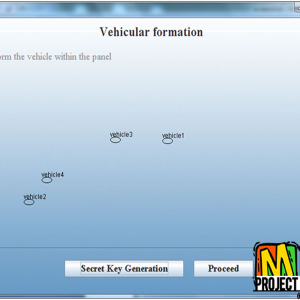
Security challenges in vehicular Cloud Abstract? In a series of recent papers, Prof. Olariu and his co-workers have promoted the vision of vehicular clouds (VCs), a nontrivial extension, along several dimensions, of conventional cloud computing. In a VC, underutilized vehicular resources including computing power, storage, and Internet connectivity can be shared between drivers or…
-
₹4,500.00
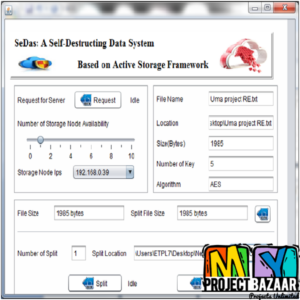
SeDas: A Self-Destructing Data System Based on Active Storage Framework Abstract? SeDas: A Self-Destructing Data System Based on Active Storage Framework. Personal data stored in the Cloud may contain account numbers, passwords, notes, and other important information that could be used and misused by a miscreant, a competitor, or a court of law. These data…
-
₹4,500.00
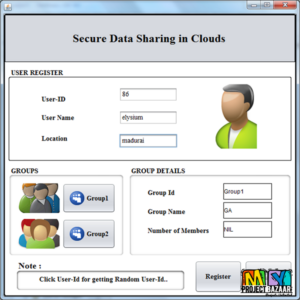
SeDaSC: Secure Data Sharing in Clouds Abstract? SeDaSC: Secure Data Sharing in Clouds. Cloud storage is an application of clouds that liberates organizations from establishing in-house data storage systems. However, cloud storage gives rise to security concerns. In case of group-shared data, the data face both cloud-specific and conventional insider threats. Secure data sharing among…
-
₹4,500.00
SeDaSC: Secure Data Sharing in Clouds Abstract? SeDaSC: Secure Data Sharing in Clouds. Cloud storage is an application of clouds that liberates organizations from establishing in-house data storage systems. However, cloud storage gives rise to security concerns. In case of group-shared data, the data face both cloud-speci?c and < Final Year Project 2016 > conventional…
-
₹4,500.00
Seed Block Algorithm A Remote Smart Data Back-up Technique for Cloud. In cloud computing, data generated in electronic form are large in amount. To maintain this data efficiently, there is a necessity of data recovery services. To cater this, in this paper we propose a smart remote data backup algorithm, Seed Block Algorithm (SBA). The…
-
₹4,500.00
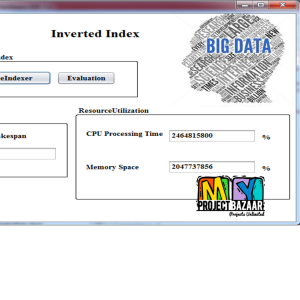
Self-Adjusting Slot Configurations for Homogeneous and Heterogeneous Hadoop Clusters Abstract? Self-Adjusting Slot Configurations for Homogeneous and Heterogeneous Hadoop Clusters. The MapReduce framework and its open source implementation Hadoop have become the defacto platform for scalable analysis on large data sets in recent years. One of the primary concerns in Hadoop is how to minimize the…
-
₹4,500.00
Self-Organized Public Key Cryptography in Mobile Ad Hoc Networks Abstract?Self-Organized Public Key Cryptography in Mobile Ad Hoc Networks Video View Demo [numbers_sections number=”1″ title=”Including =Packages=” last=”no” ] Complete Source Code Complete Documentation Complete Presentation Slides Flow Diagram Database File Screenshots Execution Procedure Readme File Addons Video Tutorials Supporting Softwares [/numbers_sections] [numbers_sections number=”2″ title=”Our =Specialization=” last=”no”…
-
₹4,500.00
Service Operator-Aware Trust Scheme for Resource Matchmaking across Multiple Clouds Abstract?A service operator-aware trust scheme SOTS for resource matchmaking across < Final Year Projects 2016 > multiple clouds. Through analyzing the built-in relationship between the users, the broker, and the service resources, this paper proposes a middleware framework of trust management that can effectively reduces…