Showing 385–396 of 468 results
-
₹5,500.00
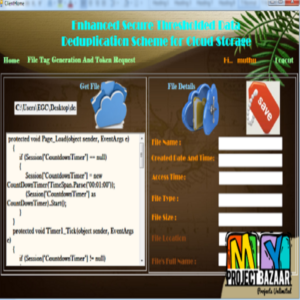
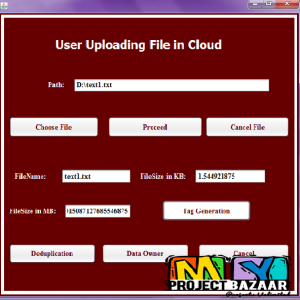
Secure Distributed Deduplication Systems with Improved Reliability Abstract? Data deduplication is a technique for eliminating duplicate copies of data, and has been widely used in cloud storage to reduce storage space and upload bandwidth. However, there is only one copy for each file stored in cloud even if such a file is owned by a…
-
₹4,500.00
Secure Distributed Deduplication Systems with Improved Reliability Abstract? Secure Distributed Deduplication Systems with Improved Reliability. Data deduplication is a technique for eliminating duplicate copies of data, and has been widely used in cloud storage to reduce storage space and upload bandwidth. However, there is only one copy for each ?le stored in cloud even if…
-
₹4,500.00
Secure k-NN Query on Encrypted Cloud Data with Multiple Keys Abstract-The k-nearest neighbors ( k-NN) query is a fundamental primitive in spatial and multimedia databases. It has extensive applications in location-based services, classification & clustering and so on. With the promise of confidentiality and privacy, massive data are increasingly outsourced to cloud in the encrypted…
-
₹4,500.00
Secure kNN Query Processing in Untrusted Cloud Environments Abstract? Secure kNN Query Processing in Untrusted Cloud Environments. Mobile devices with geo-positioning capabilities (e.g., GPS) enable users to access information that is relevant to their present location. Users are interested in querying about points of interest (POI) in their physical proximity, such as restaurants, cafes,…
-
₹4,500.00
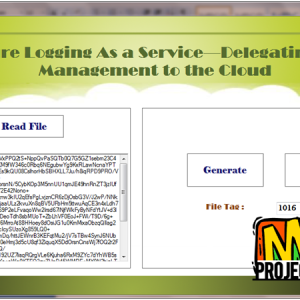
Secure Logging As a Service -Delegating Log Management to the Cloud Abstract?Secure Logging As a Service -Delegating Log Management to the Cloud. Securely maintaining log records over extended periods of time is very important to the proper functioning of any organization. Integrity of the log files and that of the logging process need to be…
-
₹4,500.00
Secure Logging As a Service?Delegating Log Management to the CloudLog files helps cyber forensic process in inquiring and seizing computer, obtaining electronic evidence for criminal investigations and maintaining computer records for the federal rules of evidence. So it can be said that logging is closely related to Forensic Computing. To make the logs permissible for…
-
₹4,500.00
Secure multi-receiver data exchange for OSNs using predicate encryption Abstract-Online Social Network is an extremely prevalent administration among utilizations of the web and distributed computing. Security assurance has turned into a noteworthy issue in light of the fact that a considerable measure of individual data is put away on the OSN stage. To make proceeded…
-
₹4,500.00
Secure Online/Offline Data Sharing Framework for Cloud-Assisted Industrial Internet of Things Abstract-Ciphertext-policy attribute-based keyword search (CP-ABKS) schemes facilitate the fine-grained keyword search over encrypted data, such as those sensed/collected from Industrial Internet of Things (IIoT) devices and stored in the cloud. However, existing CP-ABKS schemes generally have significant computation and storage requirements, which are beyond…
-
₹4,500.00
Secure Phrase Search for Intelligent Processing of Encrypted Data in Cloud-Based IoT Abstract-Phrase search allows retrieval of documents containing an exact phrase, which plays an important role in many machine learning applications for cloud-based IoT, such as intelligent medical data analytics. In order to protect sensitive information from being leaked by service providers, documents (e.g.,…
-
₹6,000.00 Original price was: ₹6,000.00.₹5,000.00Current price is: ₹5,000.00.
Secure Phrase Search for Intelligent Processing of Encrypted Data in Cloud-Based IoT Abstract-Phrase search allows retrieval of documents containing an exact phrase, which plays an important role in many machine learning applications for cloud-based IoT, such as intelligent medical data analytics. In order to protect sensitive information from being leaked by service providers, documents (e.g.,…
-
₹5,500.00
R3E: Secure, Efficient and Fine-Grained Data Access Control Mechanism for P2P Storage Cloud Abstract?Abstract By combining cloud computing and Peer-to-Peer computing, a P2P storage cloud can be formed to offer highly available storage services, lowering the economic cost by exploiting the storage space of participating users. However, since cloud severs and users are usually outside…
-
₹4,500.00
Securing Broker-Less Publish/Subscribe Systems Using Identity-Based Encryption Abstract? SThe provisioning of basic security mechanisms such as authentication and confidentiality is highly challenging in a content-based publish/subscribe system. Authentication of publishers and subscribers is difficult to achieve due to the loose coupling of publishers and subscribers. Likewise, confidentiality of events and subscriptions conflicts with content-based…