Showing 361–372 of 468 results
-
₹4,500.00
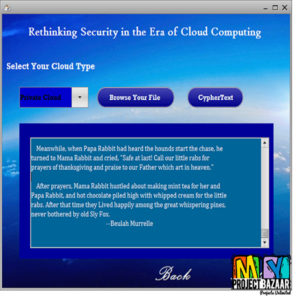
Rethinking Security in the Era of Cloud Computing Abstract– Cloud computing has emerged as a dominant platform for computing for the foreseeable future, resulting in an ongoing disruption to the way we build and deploy software. This disruption offers a rare opportunity to integrate new approaches to computer security. In this paper we outline a…
-
₹4,500.00
Revisiting Attribute-Based Encryption with Verifiable Outsourced Decryption Abstract? Revisiting Attribute-Based Encryption with Verifiable Outsourced Decryption. Attribute-based encryption < Final Year Projects 2016 > ABE [1] is a promising technique for ?ne-grained access control of encrypted data in a cloud storage, however, decryption involved in ABEs is usually too expensive for resource-constrained front-end users, which greatly…
-
₹4,500.00
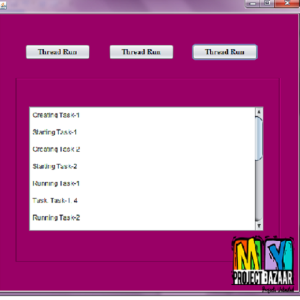
Robinhood: Towards Efficient Work-stealing in Virtualized Environments Abstract?Robinhood: Towards Efficient Work-stealing in Virtualized Environments. A common user-level task scheduler for managing and scheduling tasks of multith readed applications,suffers from inefficiency in virtualized environments, because the steal attempts of thief threads may waste CPU cycles that could be otherwise used by busy threads.This paper contributes a…
-
₹4,500.00
Robust cloud management of MANET checkpoint sessions Abstract? Robust cloud management of MANET checkpoint sessions.In a traditional mobile ad-hoc network < Final Year Projects 2016 > MANET, if two nodes are engaged in a session and one of them departs suddenly, their communication is aborted. The session is not active any more, work is lost…
-
₹4,500.00
Rollback Mechanisms for Cloud Management APIs using AI planning Abstract-Human-induced faults play a large role in systems reliability. In cloud platforms, system administrators may inadvertently make catastrophic mistakes, like deleting a virtual disk with important data. Providing rollback for cloud operations can reduce the severity and impact of such mistakes, by allowing to revert to…
-
₹5,500.00
Run Time Application Repartitioning in Dynamic Mobile Cloud Environments Abstract?Abstract As mobile computing increasingly interacts with the cloud, a number of approaches, e.g., MAUI and CloneCloud, have been proposed, aiming to offload parts of the mobile application execution to the cloud. To achieve a good performance by using these approaches, they particularly focus on the…
-
₹5,500.00
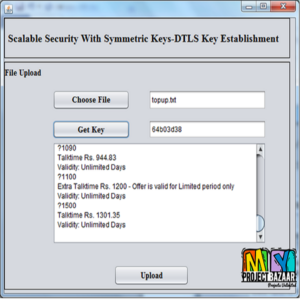
S3K: Scalable Security With Symmetric Keys?DTLS Key Establishment for the Internet of Things Abstract?Abstract DTLS is becoming the de facto standard for communication security in the Internet of Things (IoT). In order to run the DTLS protocol, one needs to establish keys between the communicating devices. The default method of key establishment requires X.509 certificates…
-
₹4,500.00
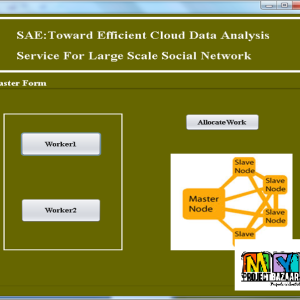
SAE: Toward Efficient Cloud Data Analysis Service for Large-Scale Social Networks Abstract? SAE: Toward Efficient Cloud Data Analysis Service for Large-Scale Social Networks. Social network analysis is used to extract features of human communities and proves to be very instrumental in a variety of scientific domains. The dataset of a social network is often so…
-
₹4,500.00
Scalable Analytics for IaaS Cloud Availability Abstract?Scalable Analytics for IaaS Cloud Availability. In a large Infrastructure-as-a-Service (IaaS) cloud, component failures are quite common. Such failures may lead to occasional system downtime and eventual violation of Service Level Agreements (SLAs) on the cloud service availability. The availability analysis of the underlying infrastructure is useful to the…
-
₹4,500.00
Scalable Recommendation with Social Contextual Information Abstract?Scalable Recommendation with Social Contextual Information. Exponential growth of information generated by online social networks demands effective and scalable recommender systems to give useful results. Traditional techniques become unqualified because they ignore social relation data; existing social recommendation approaches consider social network structure, but social contextual information has not…
-
₹4,500.00
Scalable secure sharing Personal Health Record in cloud(JSP) Abstract?Personal health record (PHR) enables patients to manage their own electronic medical records (EMR) in a centralized way, and it is often outsourced to be stored in a third-party server. In this paper we propose a novel secure and scalable system for sharing PHRs. We focus…
-
₹4,500.00
Scalable secure sharing Personal Health Record using Attribute Based Encryption Abstract? Personal health record (PHR) is an emerging patient-centric model of health information exchange, which is often outsourced to be stored at a third party, such as cloud providers. However, there have been wide privacy concerns as personal health information could be exposed to those…