Showing 373–384 of 468 results
-
₹5,500.00
SecRBAC: Secure data in the Clouds Abstract?Most current security solutions are based on perimeter security. However, Cloud computing breaks the organization perimeters. When data resides in the Cloud, they reside outside the organizational bounds. This leads users to a loos of control over their data and raises reasonable security concerns that slow down the adoption…
-
₹5,500.00
SecRBAC: Secure data in the Clouds Abstract? Most current security solutions are based on perimeter security. However, Cloud computing breaks the organization perimeters. When data resides in the Cloud, they reside outside the organizational bounds. This leads users to a loos of control over their data and raises reasonable security concerns that slow down the…
-
₹4,500.00
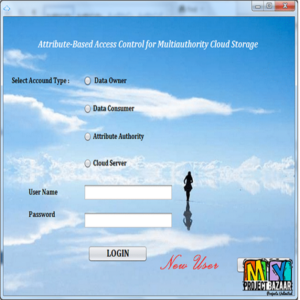
Secure and Efficient Attribute-Based Access Control for Multiauthority Cloud Storage Abstract-Cloud storage facilitates both individuals and enterprises to cost effectively share their data over the Internet.However,this also brings difficult challenges to the access control of shared data since few cloud servers can be fully trusted. Ciphertext-policy attribute-based encryption (CP-ABE) is a promising approach that enables…
-
₹4,500.00
Secure Auditing and Deduplicating Data in Cloud Abstract? Secure Auditing and Deduplicating Data in Cloud. As the cloud computing technology develops during the last decade, outsourcing data to cloud service for storage becomes an attractive trend, which bene?ts in sparing efforts on heavy data maintenance and management. Nevertheless, since the outsourced cloud storage is not…
-
₹4,500.00
Secure Authentication Using Session Based Password with Virtual Keyboard Abstract-Early people use textual passwords as a security but these passwords get affected to the various attacks like dictionary attack, shoulder surfing, etc. After the period, graphical passwords are coming to the existence but the graphical passwords have some own disadvantages such as they require more…
-
₹4,500.00
Secure Cloud Storage Meets with Secure Network Coding Abstract? Secure Cloud Storage Meets with Secure Network Coding. Reveals an intrinsic relationship between secure cloud storage and secure network coding for the first time. Secure cloud storage was proposed only recently while secure network coding has been studied for more than ten years. Although the two…
-
₹5,500.00
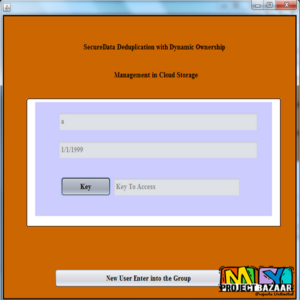
Secure Data Deduplication with Dynamic Ownership Management in Cloud Storage Abstract? In cloud storage services, deduplication technology is commonly used to reduce the space and bandwidth requirements of services by eliminating redundant data and storing only a single copy of them. Deduplication is most effective when multiple users outsource the same data to the cloud…
-
₹4,500.00
Secure Data Group Sharing and Conditional Dissemination with Multi-Owner in Cloud Computing Abstract-With the rapid development of cloud services, huge volume of data is shared via cloud computing. Although cryptographic techniques have been utilized to provide data confidentiality in cloud computing, current mechanisms cannot enforce privacy concerns over ciphertext associated with multiple owners, which makes…
-
₹4,500.00
Secure Data Group Sharing and Conditional Dissemination with Multi-Owner in Cloud Computing Abstract-With the rapid development of cloud services, huge volume of data is shared via cloud computing. Although cryptographic techniques have been utilized to provide data confidentiality in cloud computing, current mechanisms cannot enforce privacy concerns over ciphertext associated with multiple owners, which makes…
-
₹5,500.00
Secure Data Sharing in Cloud Computing Using Revocable-Storage Identity-Based Encryption Abstract? Cloud computing provides a flexible and convenient way for data sharing, which brings various benefits for both the society and individuals. But there exists a natural resistance for users to directly outsource the shared data to the cloud server since the data often contain…
-
₹4,500.00
Secure Data Storage and Searching for Industrial IoT by Integrating Fog Computing and Cloud Computing Abstract-With the fast development of Industrial Internet of Things (IIoT), a large amount of data is being generated continuously by different sources. Storing all the raw data in the IIoT devices locally is unwise considering that the end devices? energy…
-
₹5,500.00
Secure Deduplication with Efficient and Reliable Convergent Key Management Abstract?Abstract Data deduplication is a technique for eliminating duplicate copies of data, and has been widely used in cloud storage to reduce storage space and upload bandwidth. Promising as it is, an arising challenge is to perform secure deduplication in cloud storage. Although convergent encryption has…