Showing 409–420 of 468 results
-
₹4,500.00
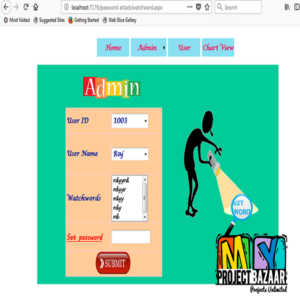
Shadow Attacks based on Password Reuses: A Quantitative Empirical Analysis Abstract-With the proliferation of websites, the security level of password-protected accounts is no longer purely determined by individual ones. Users may register multiple accounts on the same site or across multiple sites, and these passwords from the same users are likely to be the same…
-
₹4,500.00
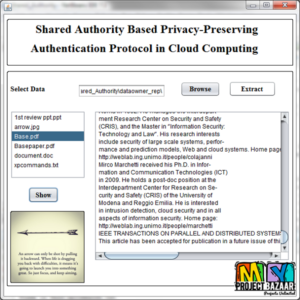
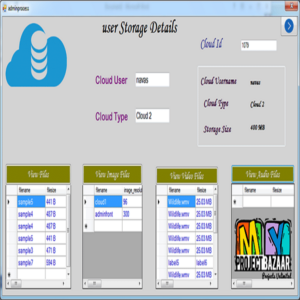
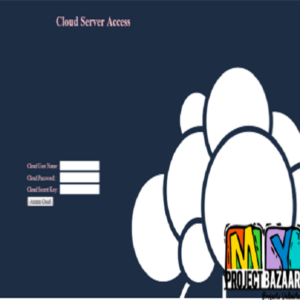
Shared Authority Based Privacy-Preserving Authentication Protocol in Cloud Computing Abstract? Shared Authority Based Privacy-Preserving Authentication Protocol in Cloud Computing. Cloud computing is an emerging data interactive paradigm to realize users? data remotely stored in an online cloud server. Cloud services provide great conveniences for the users to enjoy the on-demand cloud applications without considering the…
-
₹5,500.00
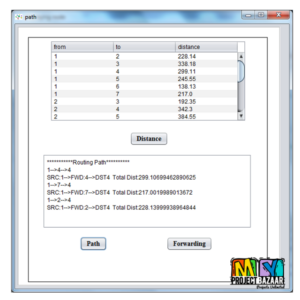
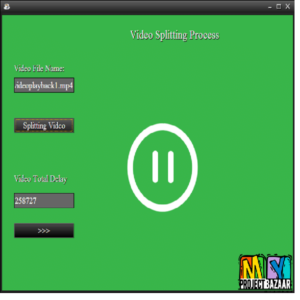
Social-Aware Video Multicast Based on Device-to-Device Communications Abstract? To meet the explosive demand on delivering high-definition video steams over cellular networks, we design a Social-aware video multiCast (SoCast) system leveraging device-to-device (D2D) communications. One salient feature of SoCast is to stimulate effective cooperation among mobile users (clients), by making use of two types of important…
-
₹4,500.00
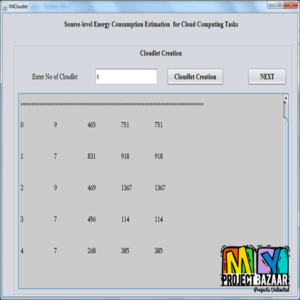
Source-level Energy Consumption Estimation for Cloud Computing Tasks Abstract– In the first place, order checking between delivery boy and the customer. If the customer order some goods in a particular company/ industry means, the order information such as customer name, address, amount, number of items to be purchased details will be sent to both customer…
-
₹4,500.00
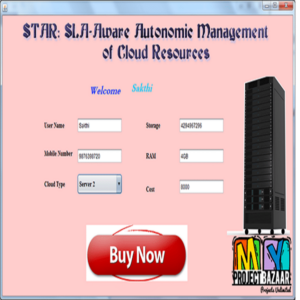
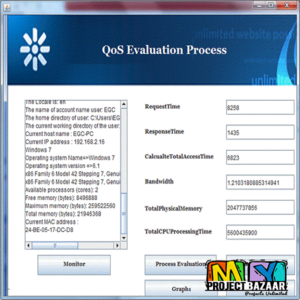
STAR: SLA-Aware Autonomic Management of Cloud Resources Abstract– Abstract?Cloud computing has recently emerged as an important service to manage applications efficiently over the Internet. Variouscloud providers offer pay per use cloud services that requires Quality of Service (QoS) management to efficiently monitor and measure the delivered services through Internet of Things (IoT) and thus needs…
-
₹4,500.00
STAR: SLA-Aware Autonomic Management of Cloud Resources Abstract– Abstract?Cloud computing has recently emerged as an important service to manage applications efficiently over the Internet. Various cloud providers offer pay per use cloud services that requires Quality of Service (QoS) management to efficiently monitor and measure the delivered services through Internet of Things (IoT) and thus…
-
₹4,500.00
Automobile Spare Shop(Android App) Abstract-Forecasts predict that Internet traffic will continue to grow in the near future. A huge share of this traffic is caused by multimedia streaming. The quality of experience (QoE) of such streaming services is an important aspect and in most cases the goal is to maximize the bit rate which?in some…
-
₹4,500.00
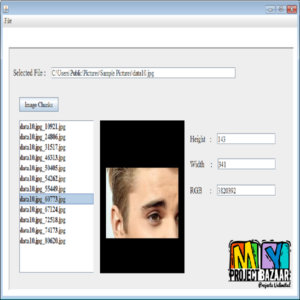
Steganography Based Content Retrieval in Cloud Computing Abstract-In a Cloud Security is updated for each and every day in an cloud environment the Security is updated for all type of cloud environments in our process focused on Cloud image Security In Recent years the some popular celebrities personal images are leaked from some social media…
-
₹4,500.00
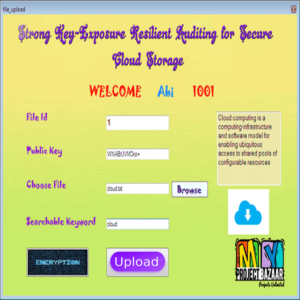
Strong Key-Exposure Resilient Auditing for Secure Cloud Storage Abstract– Key exposure is one serious security problem for cloud storage auditing. In order to deal with this problem, cloud storage auditing scheme with key-exposure resilience has been proposed. However, in such a scheme, the malicious cloud might still forge valid authenticators later than the key-exposure time…
-
₹5,500.00
Supporting Multi Data Stores Applications in Cloud Environments Abstract?Abstract The production of huge amount of data and the emergence of cloud computing have introduced new requirements for data management. Many applications need to interact with several heterogeneous data stores depending on the type of data they have to manage: traditional data types, documents, graph data…
-
₹4,500.00
Swiper: Exploiting Virtual Machine Vulnerability in Third-Party Abstract?Swiper: Exploiting Virtual Machine Vulnerability in Third-Party. The emerging paradigm of cloud computing, e.g., Amazon Elastic Compute Cloud (EC2), promises a highly flexible yet robust environment for large-scale applications. Ideally, while multiple virtual machines (VM) share the same physical resources (e.g., CPUs, caches, DRAM, and I/O devices), <...
-
₹4,500.00
System of Systems for Quality-of-Service Observation and Response in Cloud Computing Environments Abstract? System of Systems for Quality-of-Service Observation and Response in Cloud Computing Environments. As military, academic, and commercial computing systems evolve from autonomous entities that deliver computing products into network centric enterprise systems that deliver computing as a service, opportunities emerge to consolidate…