Showing 457–468 of 468 results
-
₹5,500.00
Using Crowdsourcing to Provide QoS for Mobile Cloud Computing Abstract? Quality of cloud service (QoS) is one of the crucial factors for the success of cloud providers in mobile cloud computing. Context-awareness is a popular method for automatic awareness of the mobile environment and choosing the most suitable cloud provider. Lack of context information may…
-
₹4,500.00
Using Data Mining Techniques for Detecting Terror-Related Activities on the Web Abstract? Using Data Mining Techniques for Detecting Terror-Related Activities on the Web. An innovative knowledge-based methodology for terrorist detection by using Web traffic content as the audit information is presented. The proposed methodology learns the typical behavior (?profile?) of terrorists by applying a data…
-
₹4,500.00
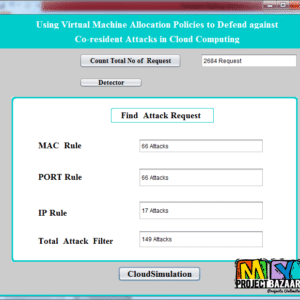
Using Virtual Machine Allocation Policies to Defend against Co-resident Attacks in Cloud Computing Abstract? Using Virtual Machine Allocation Policies to Defend against Co-resident Attacks in Cloud Computing. Cloud computing enables users to consume various < Final Year Projects 2016 > IT resources in an on-demand manner, and with low management overhead. However, customers can face…
-
₹4,500.00
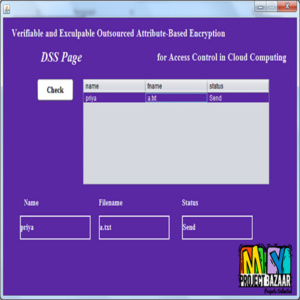
Verifiable and Exculpable Outsourced Attribute-Based Encr yption for Access Control in Cloud Computing Abstract-In the first place, propose two ciphertext-policy attribute-based key encapsulation mechanism (CP-AB-KEM) schemes that for the first time achieve both outsourced encryption and outsourced decryption in two system storage models and give corresponding security analysis. In our schemes, heavy computations are outsourced…
-
₹4,500.00
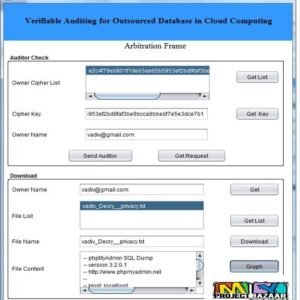
Verifiable Auditing for Outsourced Database in Cloud Computing Abstract? Verifiable Auditing for Outsourced Database in Cloud Computing. The notion of database outsourcing enables the data owner to delegate the database management to a cloud service provider < Final Year Projects 2016 > CSP that provides various database services to different users. Recently, plenty of research…
-
₹4,500.00
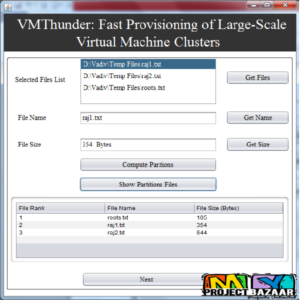
VMThunder: Fast Provisioning of Large-Scale Virtual Machine Clusters Abstract? VMThunder: Fast Provisioning of Large-Scale Virtual Machine Clusters. Infrastructure as a service (IaaS) allows users to rent resources from the Cloud to meet their various computing requirements. The pay-as-you-use model, however, poses a nontrivial technical challenge to the IaaS cloud service providers: how to fast provision…
-
₹4,500.00
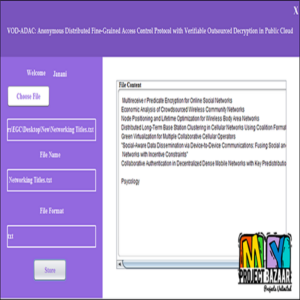
VOD-ADAC: Anonymous Distributed Fine-Grained Access Control Protocol with Verifiable Outsourced Decryption in Public Cloud Abstract– Remote data access control is of crucial importance in public cloud. Based on its own inclinations, the data owner predefines the access policy. When the user satisfies the data owner?s access policy, it has the right to access the data…
-
₹5,500.00
White-Box Traceable CP-ABE for Cloud Storage Service: How to Catch People Leaking Their Access Credentials Effectively Abstract-Ciphertext-policy attribute-based encryption (CP-ABE) has been proposed to enable fine-grained access control on encrypted data for cloud storage service. In the context of CP-ABE, since the decryption privilege is shared by multiple users who have the same attributes, it…
-
₹5,500.00
Workflow Transformation for Real-Time Big Data Processing Abstract?Abstract With the explosion of big data, processing and analyzing large numbers of continuous data streams in real-time,such as social media stream, sensor data streams, log streams,stock exchanges streams, etc., has become a crucial requirement for many scientific and industrial applications in recent years.Increased volume of streaming data…
-
₹4,500.00
Workload modeling for resource usage analysis and simulation in cloud computing Abstract-In the first place, workload modeling enables performance analysis and simulation of cloud resource management policies, which allows cloud providers to improve their systems? Quality of Service (QoS) and researchers to evaluate new policies without deploying expensive large scale environments. However, workload modeling is…
-
₹4,500.00
Workload-Based Software Rejuvenation in Cloud Systems Abstract? Workload-Based Software Rejuvenation in Cloud Systems. Video View Demo [numbers_sections number=”1″ title=”Including =Packages=” last=”no” ] Complete Source Code Complete Documentation Complete Presentation Slides Flow Diagram Database File Screenshots Execution Procedure Readme File Addons Video Tutorials Supporting Softwares [/numbers_sections] [numbers_sections number=”2″ title=”Our =Specialization=” last=”no” ] Voice Conference Video On…
-
₹4,500.00
Wormhole: The Hidden Virus Propagation Power of a Search Engine in Social Networks Abstract-Today search engines are tightly coupled with social networks, and present users with a double-edged sword: they are able to acquire information interesting to users but are also capable of spreading viruses introduced by hackers. It is challenging to characterize how a…