Showing 133–144 of 147 results
-
₹4,500.00
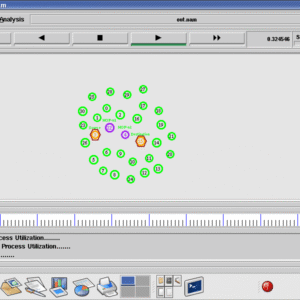
Security Enhancements for Mobile Ad Hoc Networks With Trust Management Using Uncertain Reasoning Abstract?The distinctive features of mobile ad hoc networks< Final Year Projects 2016 > including dynamic topology and open wireless medium, may lead to MANETs suffering from many security vulnerabilities. In this paper, using recent advances in uncertain reasoning that originated from the…
-
₹5,500.00
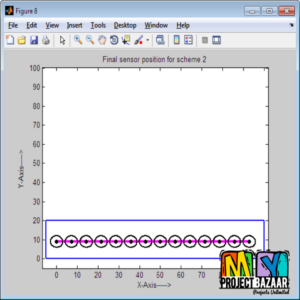
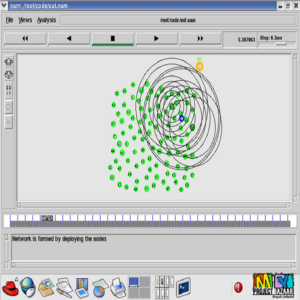
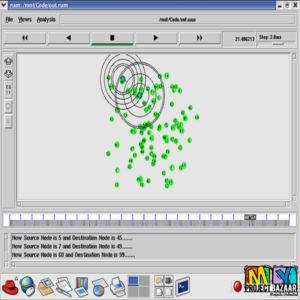
Self-Deployment of Randomly Scattered Mobile Sensors to Achieve Barrier Coverage Abstract? Constructing sensor barrier is a critical issue in wireless sensor networks for military and homeland security applications, which aims to detect intruders crossing into a protected area. In this letter, we propose two distributed, localized deployment schemes for self-adjustment of randomly deployed mobile sensor…
-
₹5,500.00
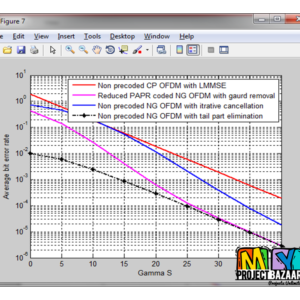
Spectrally Precoded OFDM Without Guard Insertion Abstract? Orthogonal frequency-division multiplexing (OFDM) signaling format is commonly associated with guard subintervals to reject interblock interference (IBI) and enable simple onetap frequency-domain equalization (FDE) at the receiver when received over dispersive channels. Despite the advantages, the insertion of guard subintervals expands the signal spectrum and thus trades off…
-
₹4,500.00
Spectrum Efficiency Improvement for Quasi-Constant Envelope OFDM Abstract-Benefiting from low peak-to-average power ratio (PAPR), constant envelope OFDM (CE-OFDM) is a promising technique in coherent optical communication. However, the spectrum efficiency of CE-OFDM is only half of conventional coherent optical OFDM, which restricts its application. We proposed a novel quasi-constant envelope OFDM (Quasi-CE-OFDM) scheme with in-phase/quadrature…
-
₹4,500.00
Successive Interference Mitigation in Multiuser MIMO Channels Abstract? Successive Interference Mitigation in Multiuser MIMO Channels. Motivated by the work of Dahrouj and Yu in applying the Han-Kobayashi transmission strategy for mitigating the intercell interference in a multi-cell multi-user multiple-input single-output Interference network MISO IN, < Final Year Projects 2016 > this paper considers splitting messages…
-
₹4,500.00
SWIMMING: Seamless and Efficient WiFi-Based Internet Access from Moving Vehicless Abstract? SWIMMING: Seamless and Efficient WiFi-Based Internet Access from Moving Vehicless. Demand for Internet access from moving vehicles has been rapidly growing. Meanwhile, the overloading issue of cellular networks is escalating due to mobile data explosion. Thus, WiFi networks are considered as a promising technology…
-
₹4,500.00
The Beauty of the Commons: Optimal Load Sharing by Base Station Hopping in Wireless Sensor Networks Abstract? The Beauty of the Commons: Optimal Load Sharing by Base Station Hopping in Wireless Sensor Networks. In wireless sensor networks < WSNs >, the base station (BS) is a critical sensor node whose failure causes severe data losses….
-
₹4,500.00
The Mason Test: A Defense Against Sybil Attacks in Wireless Networks Without Trusted Authorities Abstract?The Mason Test: A Defense Against Sybil Attacks in Wireless Networks WithoutTrusted Authorities. Wireless networks are vulnerable to Sybil attacks, in which a malicious node poses as many identities in order to gain disproportionate in?uence. Many defenses based on spatial variability…
-
₹4,500.00
The Role of Location Popularity in Multicast Mobile Ad Hoc Networks Abstract? The Role of Location Popularity in Multicast Mobile Ad Hoc Networks. In the asymptotic analysis of large scale mobile networks, most previous works assume that nodes move in all the cells identically. We put forward this line of research by considering location popularity,…
-
₹4,500.00
The study and application of the improved region growing algorithm for liver segmentation Abstract?The study and application of the improved region growing algorithm for liver segmentation. In order to improve the accuracy of the medical image segmentation and reduce the effect of selecting seed points using region growing algorithm, an improved region growing method is…
-
₹5,500.00
Towards Distributed Optimal Movement Strategy for Data Gathering in Wireless Sensor Networks Abstract? To design a distributed movement strategy for mobile collectors, which can be either physical mobile agents or query/collector packets periodically launched by the sink, to achieve successful data gathering in wireless sensor networks. Formulating the problem as general random walks on a…
-
₹4,500.00
Traffic Decorrelation Techniques for Countering a Global Eavesdropper in WSNs Abstract-In the first place, address the problem of preventing the inference of contextual information in event-driven wireless sensor networks (WSNs). The problem is considered under a global eavesdropper who analyzes low-level RF transmission attributes, such as the number of transmitted packets, inter-packet times, and traffic…