Showing 121–132 of 147 results
-
₹4,500.00
Privacy Protection for Wireless Medical Sensor Data Abstract? wireless sensor networks have been widely used in healthcare applications, such as hospital and home patient monitoring. Wireless medical sensor networks are more vulnerable ready < Final Year Projects 2016 > to eavesdropping, modi?cation, impersonation and replaying attacks than the wired networks. A lot of work has…
-
₹5,500.00
Proactive spectrum handoff protocol for cognitive radio ad hoc network and analytical evaluation Abstract?Abstract Spectrum handoff in cognitive radio technology has been emerged as a new method for improving performance of the cognitive radio networks. The authors propose a proactive spectrum handoff protocol based on a single rendezvous (SRV) coordination scheme without common control channel….
-
₹4,500.00
PSR: A Lightweight Proactive Source Routing Protocol For Mobile Ad Hoc Networks Abstract?Opportunistic data forwarding has drawn much attention in the research community of multihop wireless networking, with most research conducted for stationary wireless networks. One of the reasons why opportunistic data forwarding has not been widely utilized in mobile ad hoc networks (MANETs) is…
-
₹5,500.00
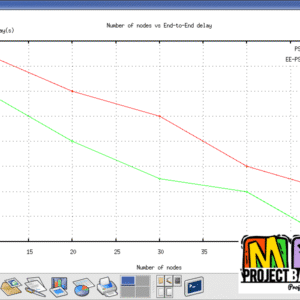
R3E: Reliable Reactive Routing Enhancement for Wireless Sensor Networks Abstract?Abstract Providing reliable and efficient communication under fading channels is one of the major technical challenges in wireless sensor networks (WSNs), especially in industrial WSNs (IWSNs) with dynamic and harsh environments. In this work,we present the Reliable Reactive Routing Enhancement (R3E) to increase the resilience to…
-
₹5,500.00
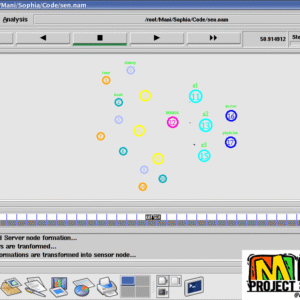
Reliable and Efficient Data Acquisition in Wireless Sensor Networks in the Presence of Transfaulty Nodes Abstract? A collection of spatially distributed sensor nodes in a wireless sensor network (WSN) work collaboratively to sense the physical phenomena around them and then send the sensed information to the s ink node through single-hop or multihop paths. In…
-
₹4,500.00
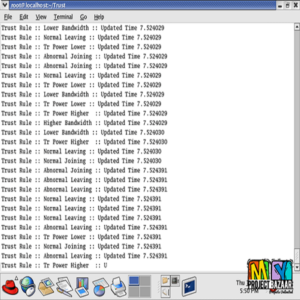
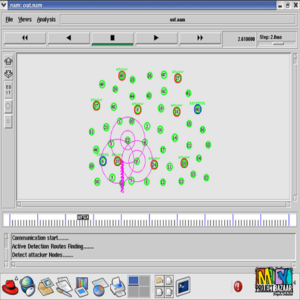
Research on Trust Sensing Based Secure Routing Mechanism for Wireless Sensor Network Abstract-In the first place, aiming at the serious impact of the typical network attacks caused by the limited energyand the poor deployment environment of wireless sensor network (WSN) on data transmission, a trust sensing-based secure routing mechanism (TSSRM) with the lightweight characteristics and…
-
₹4,500.00
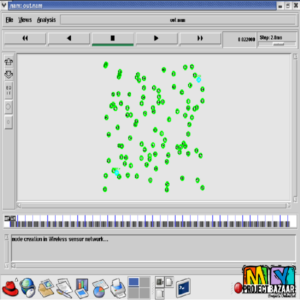
Secure and Distributed Data Discovery and Dissemination in Wireless Sensor Networks Abstract? A data discovery and dissemination protocol for wireless sensor networks WSNs < Final Year Projects 2016 > is responsible for updating con?guration parameters of, and distributing management commands to, the sensor nodes. All existing data discovery and dissemination protocols suffer from two drawbacks….
-
₹5,500.00
Secure Communication in Uplink Transmissions: User Selection and Multiuser Secrecy Gain Abstract?secure communications in uplink transmissions, where there are a base station (BS) with M receive antennas, K mobile users each with a single antenna, and an eavesdropper with N receive antennas. < final year projects > [numbers_sections number=”1″ title=”Including =Packages=” last=”no” ] Complete Source…
-
₹4,500.00
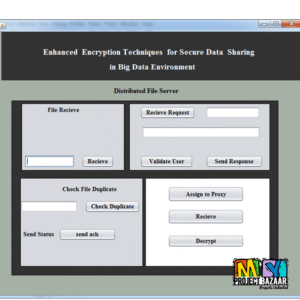
Secure Data Aggregation Technique for Wireless Sensor Networks in the Presence of Collusion Attacks Abstract? Secure Data Aggregation Technique for Wireless Sensor Networks in the Presence of Collusion Attacks. Due to limited computational power and energy resources, aggregation of data from multiple sensor nodes done at the aggregating node is usually accomplished by simple methods…
-
₹5,500.00
Secure Routing for Mobile Ad hoc Networks Abstract?Abstract technology advocates self-organized wireless interconnection of communication devices that would either extend or operate in concert with the wired networking infrastructure or, possibly,evolve to autonomous networks. In either case, the proliferation of MANET-based applications depends on a multitude of factors, with trustworthiness being one of the primary…
-
₹4,500.00
Secure Signature-Based Authenticated Key Establishment Scheme for Future IoT Applications Abstract– Internet of Things (IoT) is a network of all devices that can be accessed through the internet. These devices can be remotely accessed and controlled using existing network infrastructure, thus allowing a direct integration of computing systems with the physical world. This also reduces…
-
₹4,500.00
SecureMAC: Securing Wireless Medium Access Control Against Insider Denial-of-Service Attacks Abstract-Wireless network dynamically allocates channel resources to improve spectral efficiency and, to avoid collisions, has its users cooperate with each other using a medium access control (MAC) protocol. However, MAC assumes user compliance and can be detrimental when a user misbehaves. An attacker who compromised…