Vulnerable Concealed Map-Reading Inside Mobile Ad Hoc Networks
₹4,500.00
- Estimated Delivery : Up to 4 business days
- Free Shipping & Returns : On all orders over $200
Vulnerable Concealed Map-Reading Inside Mobile Ad Hoc Networks
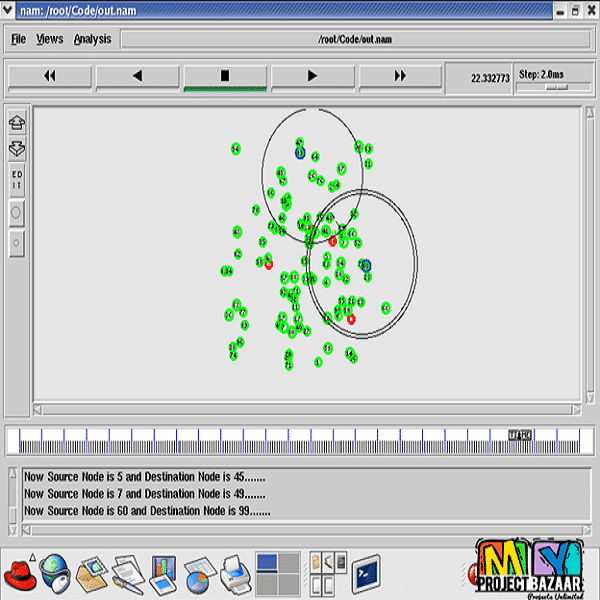
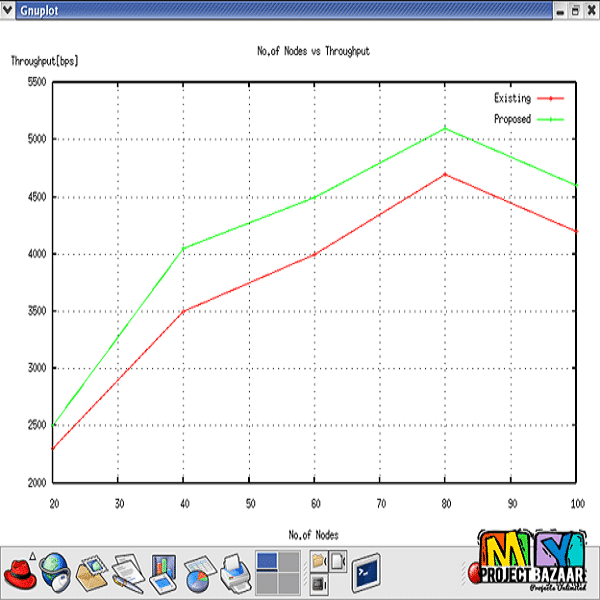
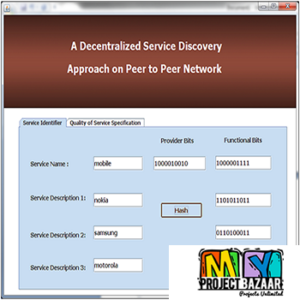
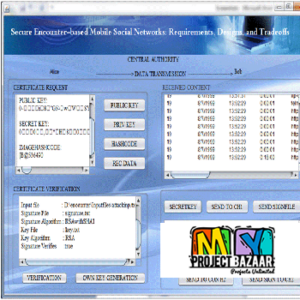
Abstract-Number of techniques has been used based on packet encryption to protect the data forwarding in MANETs, Still MANETs are attacked by hackers. To get over these attack a new technique called statistical traffic pattern discovery system can be used. It is an approach to discover entire raw traffic by using probability of traffic characteristics. It discover the relationships of source to destination communication. Maximum in wireless ad hoc network, it will always choose shortest path in prior. So attackers shall enter the network freely, because if the node monitors the packet forwarding mechanism it can easily identify the entire traffic pattern in the system. Based on the activity of hacker will enter the network effectively. It can be helpful for dropping or modifying data. But here we choose the second shortest path for data forwarding. In our scenario when we change to select the routing path hackers can?t be capture the current routing path.
[numbers_sections number=”1″ title=”Including =Packages=” last=”no” ]
[/numbers_sections]
[numbers_sections number=”2″ title=”Our =Specialization=” last=”no” ]
[/numbers_sections]
[numbers_sections number=”3″ title=”Support =Service=” last=”yes” ]
[/numbers_sections]
[one_third class=”” last=”no” ]
[banner width=”0″ height=”92″ url=”#” target=”no” title=”CUSTOMER SUPPORT” subtitle=”Call us +91 96777 61440″ title_size=”16″ title_size_hover=”10″ subtitle_size=”12″ subtitle_size_hover=”17″ icon_size=”38″ icon_size_hover=”52″ background=”” background_image=”” border=”#d0cece” color_icon=”#a1a1a1″ color_title=”#000000″ color_subtitle=”#666464″ background_hover=”#464646″ border_hover=”” color_icon_hover=”#f09d0c” color_title_hover=”#d0cece” color_subtitle_hover=”#fff” type=”switch-text” icon=”phone” style=”no” ]
[/one_third]
[one_third class=”” last=”no” ]
[banner width=”0″ height=”92″ url=”http://myprojectbazaar.com/testimonial/” target=”no” title=”HAPPY CUSTOMERS” subtitle=”Read the testimonials” title_size=”16″ title_size_hover=”10″ subtitle_size=”12″ subtitle_size_hover=”17″ icon_size=”35″ icon_size_hover=”50″ background=”” background_image=”” border=”#d0cece” color_icon=”#a1a1a1″ color_title=”#000000″ color_subtitle=”#666464″ background_hover=”#464646″ border_hover=”” color_icon_hover=”#f09d0c” color_title_hover=”#d0cece” color_subtitle_hover=”#fff” type=”switch-text” icon=”comments-alt” style=”no” ]
[/one_third]
[one_third class=”” last=”yes” ]
[banner width=”0″ height=”92″ url=”http://myprojectbazaar.com/blogs/” target=”no” title=”LATEST NEWS” subtitle=”enjoy our blog” title_size=”16″ title_size_hover=”10″ subtitle_size=”12″ subtitle_size_hover=”17″ icon_size=”35″ icon_size_hover=”50″ background=”” background_image=”” border=”#d0cece” color_icon=”#a1a1a1″ color_title=”#000000″ color_subtitle=”#666464″ background_hover=”#464646″ border_hover=”” color_icon_hover=”#f09d0c” color_title_hover=”#d0cece” color_subtitle_hover=”#fff” type=”switch-text” icon=”bullhorn” style=”no” ]
[/one_third]
[space][clear]
[box_title ]Statistical Report[/box_title]
[random_numbers icon=”http://myprojectbazaar.com/wp-content/uploads/2013/12/110.jpg” text=”satisfied customers” number=”3,589″ last=”no” ][random_numbers icon=”http://myprojectbazaar.com/wp-content/uploads/2013/12/25.jpg” text=”Freelance projects” number=”983″ last=”no” ][random_numbers icon=”http://myprojectbazaar.com/wp-content/uploads/2013/12/311.jpg” text=”sales on Site” number=”11,021″ last=”no” ][random_numbers icon=”http://myprojectbazaar.com/wp-content/uploads/2013/12/41.jpg” text=”developers” number=”175+” last=”yes” ]
[space][clear]
| Domains | Mobile Computing |
|---|---|
| Programming Language | NS2 |