
Using Data Mining Techniques for Detecting Terror-Related Activities on the Web
Product Description
Using Data Mining Techniques for Detecting Terror-Related
Activities on the Web
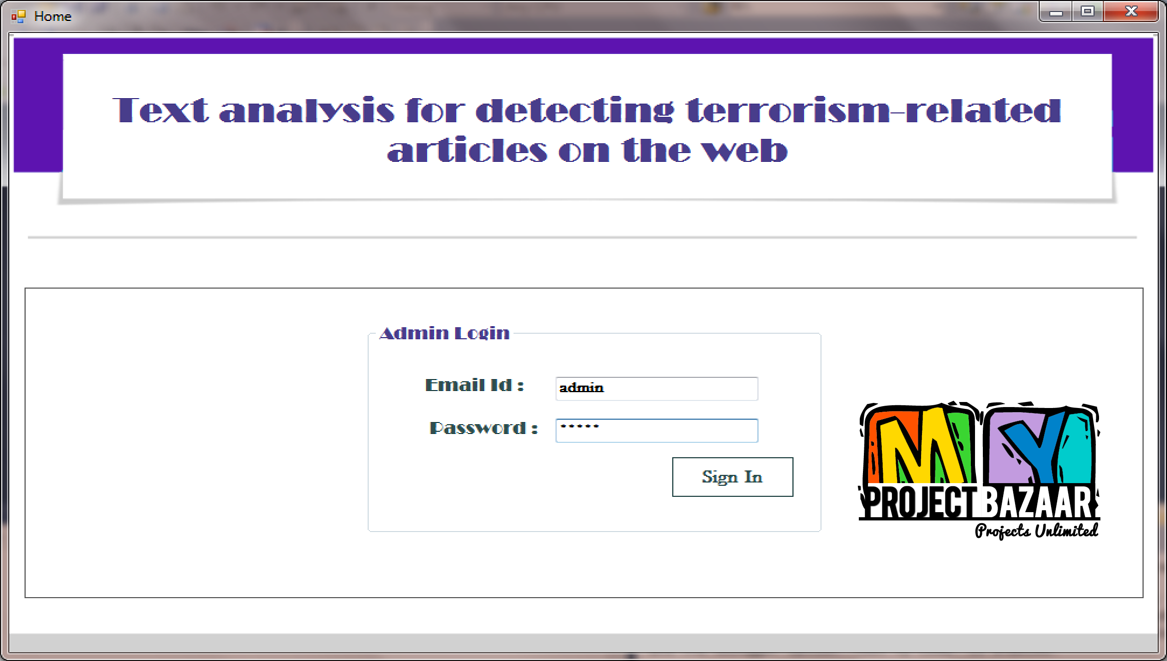
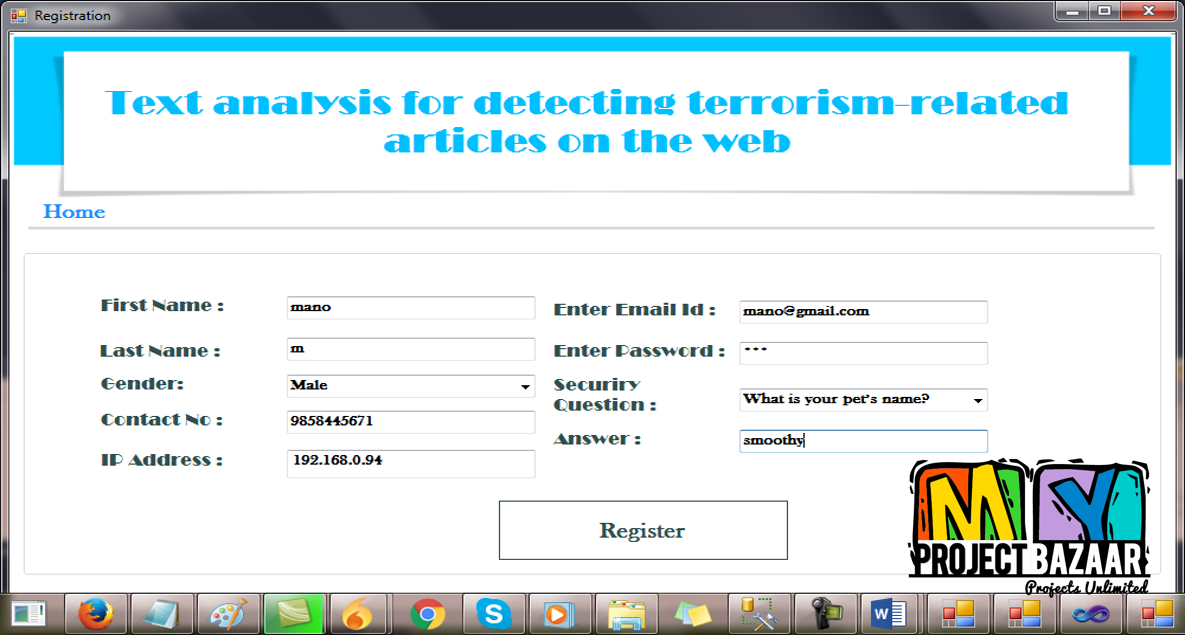
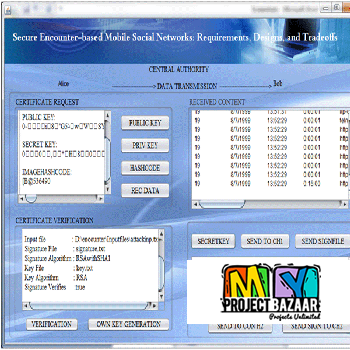
Abstract— Using Data Mining Techniques for Detecting Terror-Related Activities on the Web. An innovative knowledge-based methodology for terrorist detection by using Web traffic content as the audit information is presented. The proposed methodology learns the typical behavior (‘profile’) of terrorists by applying a data mining algorithm to the textual content of terror-related Web sites. The resulting profile is used by the system to perform real-time detection of users suspected of being engaged in terrorist activities. The Receiver-Operator Characteristic (ROC) analysis shows that this methodology can outperform a command based intrusion detection System. Terrorist cells are using the Internet infrastructure to exchange information and recruit new members and supporters Lemos 2002; Kelley 2002. < Final Year Projects 2016 > For example, high-speed Internet connections were used intensively by members of the infamous ‘Hambu rg Cell’ that was largely responsible for the preparation of the September 11 attacks against the United States (Corbin 2002). This is one reason for the major effort made by law enforcement agencies around the world in gathering information from the Web about terror-related activities. It is believed that the detection of terrorists on the Web might prevent further terrorist attacks (Kelley 2002).
Including Packages
Our Specialization
Support Service
Statistical Report

satisfied customers
3,589
Freelance projects
983
sales on Site
11,021
developers
175+Additional Information
| Domains | |
|---|---|
| Programming Language |
Would you like to submit yours?














There are no reviews yet