Shadow Attacks based on Password Reuses: A Quantitative Empirical Analysis
Product Description
Shadow Attacks based on Password Reuses: A Quantitative Empirical Analysis
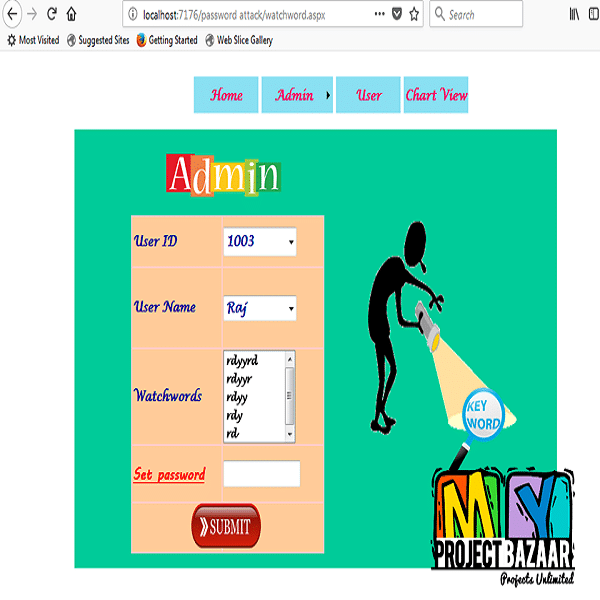
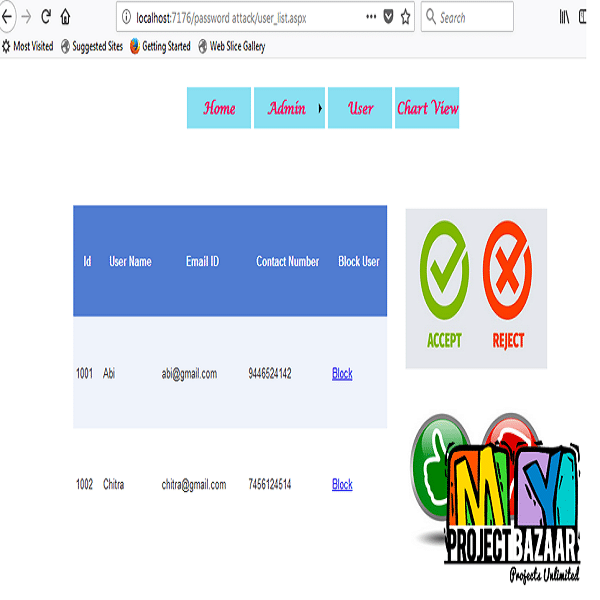
Abstract-With the proliferation of websites, the security level of password-protected accounts is no longer purely determined by individual ones. Users may register multiple accounts on the same site or across multiple sites, and these passwords from the same users are likely to be the same or similar. As a result, an adversary can compromise the account of a user on a web forum, then guess the accounts of the same user in sensitive accounts, e.g., online banking services, whose accounts could have the same or even stronger passwords. We name this attack as the shadow attack on passwords. To understand the situation, we examined the stateof-the-art Intra-Site Password Reuses (ISPR) and Cross-Site Password Reuses (CSPR) based on the leaked passwords from the biggest Internet user group (i.e., 668 million members in China). With a collection of about 70 million real-world web passwords across
four large websites in China, we obtained around 4.6 million distinct users who have multiple accounts on the same site or across different sites. Here found that for the users with multiple accounts in a single website, 59.72% reused their passwords and for the users with multiple accounts on multiple websites, 33.16 ± 8.91% reused their passwords across websites. For the users that have multiple accounts but different passwords, the set of passwords of the same user exhibits patterns that can help password guessing: a leaked weak password reveals partial information of a strong one, which degrades the strength of the strong one. Given the aforementioned findings and conducted an experiment and achieved a 39.38% improvement of guessing success rate with John the Ripper guessing tool. To the best of our knowledge and are the first to provide a large-scale, empirical, and quantitative measurement of web password
reuses, especially ISPR, and shed light on the severity of such threat in the real world.
Including Packages
Our Specialization
Support Service
Statistical Report

satisfied customers
3,589
Freelance projects
983
sales on Site
11,021
developers
175+Additional Information
| Domains | |
|---|---|
| Programming Language |