Secure Signature-Based Authenticated Key Establishment Scheme for Future IoT Applications
Product Description
Secure Signature-Based Authenticated Key
Establishment Scheme for Future IoT Applications
Abstract– Internet of Things (IoT) is a network of all devices that can be accessed through the internet. These devices can be remotely accessed and controlled using existing network infrastructure, thus allowing a direct integration of computing systems with the physical world. This also reduces human involvement along with improving accuracy, efficiency and resulting in economic benefit. The devices in IoT facilitate the day to
day life of people. However, IoT has an enormous threat to security and privacy due to its heterogeneous and dynamic
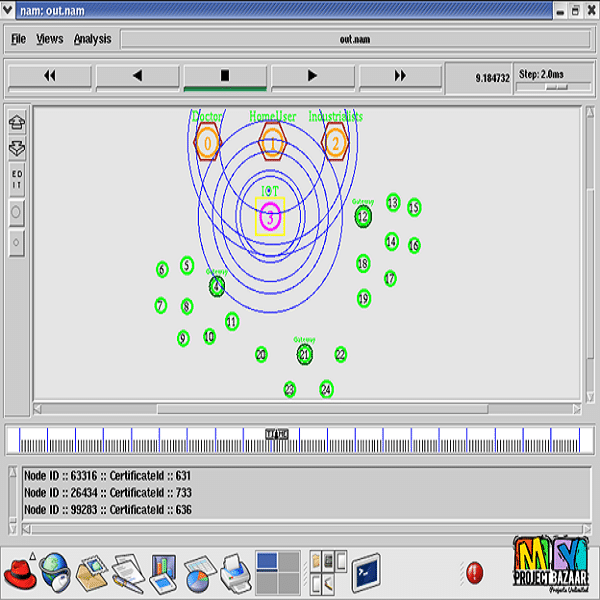
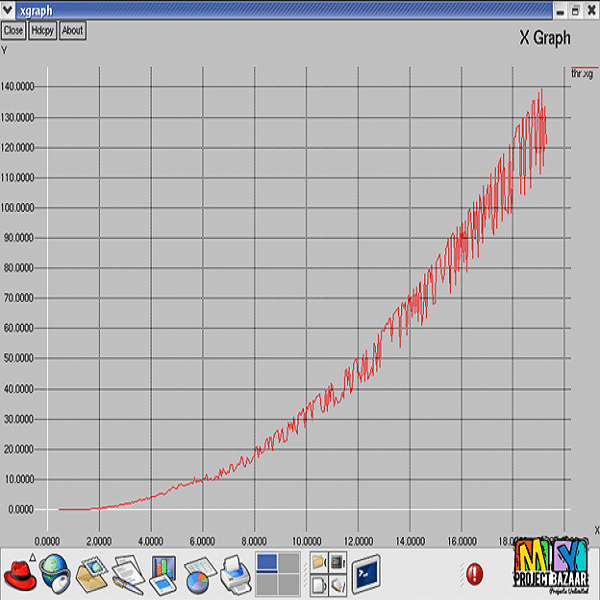
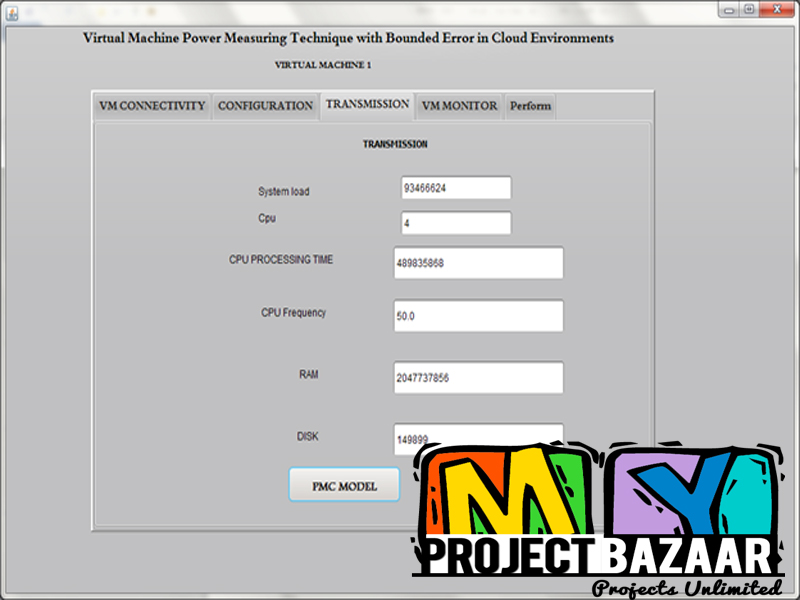
nature. Authentication is one of the most challenging security requirements in IoT environment, where a user (external party) can directly access information from the devices, provided the mutual authentication between user and devices happens. In this paper, we present a new signature-based authenticated key establishment scheme for IoT environment. The proposed scheme is tested for security with the help of the widely-used Burrows-Abadi-Needham logic (BAN logic), informal security analysis, and also the formal security verification using the broadly-accepted Automated Validation of Internet Security Protocols and Applications (AVISPA) tool. The proposed scheme is also implemented using the widely-accepted NS2 simulator, and the simulation results demonstrate the practicability of the
scheme. Finally, the proposed scheme provides more functionality features, and its computational and communication costs are also comparable with other existing approaches.
Including Packages
Our Specialization
Support Service
Statistical Report

satisfied customers
3,589
Freelance projects
983
sales on Site
11,021
developers
175+