
The Mason Test: A Defense Against Sybil Attacks in Wireless Networks Without Trusted Authorities
Product Description
The Mason Test: A Defense Against Sybil
Attacks in Wireless Networks Without
Trusted Authorities
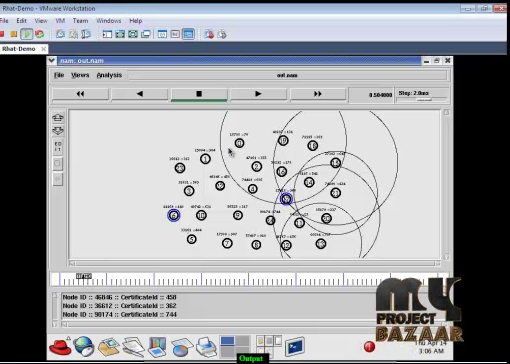
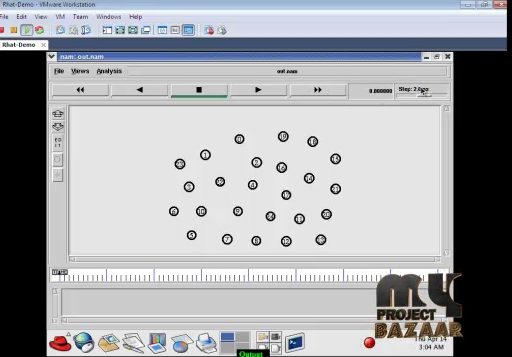
Abstract—The Mason Test: A Defense Against Sybil Attacks in Wireless Networks WithoutTrusted Authorities. Wireless networks are vulnerable to Sybil attacks, in which a malicious node poses as many identities in order to gain disproportionate influence. Many defenses based on spatial variability of wireless channels exist, but depend either on detailed, multi-tap channel estimation—something not exposed on commodity 802.11 devices—or valid RSSI observations from multiple trusted sources, e.g., corporate access points—something not directly available in ad hoc and elay-tolerant networks with potentially malicious neighbors. We extend these techniques to be practical for wireless ad hoc networks of commodity 802.11 devices. Specifically, we propose two efficient methods for separating the valid < Final Year Projects 2016 > observations of behaving nodes from those falsified by malicious participants. Further, we note that prior signal print methods are easily defeated by mobile attackers and develop an appropriate challenge-response defense. Finally, we present the Mason test, the first implementation of these techniques for ad hoc and delay-tolerant networks of commodity 802.11 devices. We illustrate its performance in several real-world scenarios.
Including Packages
Our Specialization
Support Service
Statistical Report

satisfied customers
3,589
Freelance projects
983
sales on Site
11,021
developers
175+Would you like to submit yours?












There are no reviews yet