Identifying and Addressing Reachability and Policy Attacks in “Secure” BGP
Product Description
Identifying and Addressing Reachability and Policy Attacks in “Secure” BGP
Abstract—Abstract BGP is known to have many security vulnerabilities due to the very nature of its underlying assumptions of trust among independently operated networks. Most prior efforts have focused on attacks that can be addressed using traditional cryptographic techniques to ensure authentication or integrity, e.g., BGPSec and related works. Although augmenting BGP with authentication and integrity mechanisms is critical, they are, by design, far from sufficient to prevent attacks based on manipulating the complex BGP protocol itself. In this paper, we identify two serious attacks on two of the most fundamental goals of BGP—to ensure reachability and to enable ASes to pick routes available to them according to their routing policies—even in the presence of BGPSec-like mechanisms.Our key contributions are to formalize a series of critical security properties,experimentally validate using commodity router implementations that BGP fails to achieve those properties,quantify the extent of these vulnerabilities in the Internet’s AS topology, and propose simple modifications to provably ensure that those properties are satisfied. Our experiments show that,using our attacks, a single malicious AS can cause thousands of other ASes to become disconnected from thousands of other ASes for arbitrarily long, while our suggested modifications almost completely eliminate such attacks.
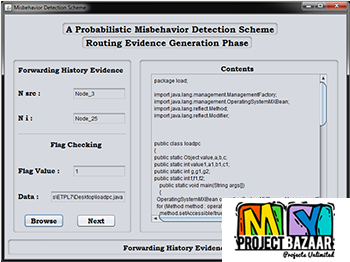
Including Packages
Our Specialization
Support Service
Statistical Report

satisfied customers
3,589
Freelance projects
983
sales on Site
11,021
developers
175+Additional Information
| Domains | |
|---|---|
| Programming Language |