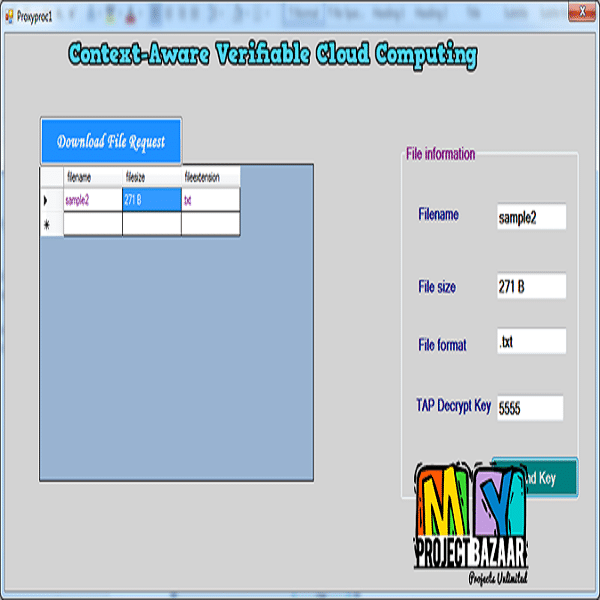
Context-Aware Verifiable Cloud Computing
Product Description
Context-Aware Verifiable Cloud Computing
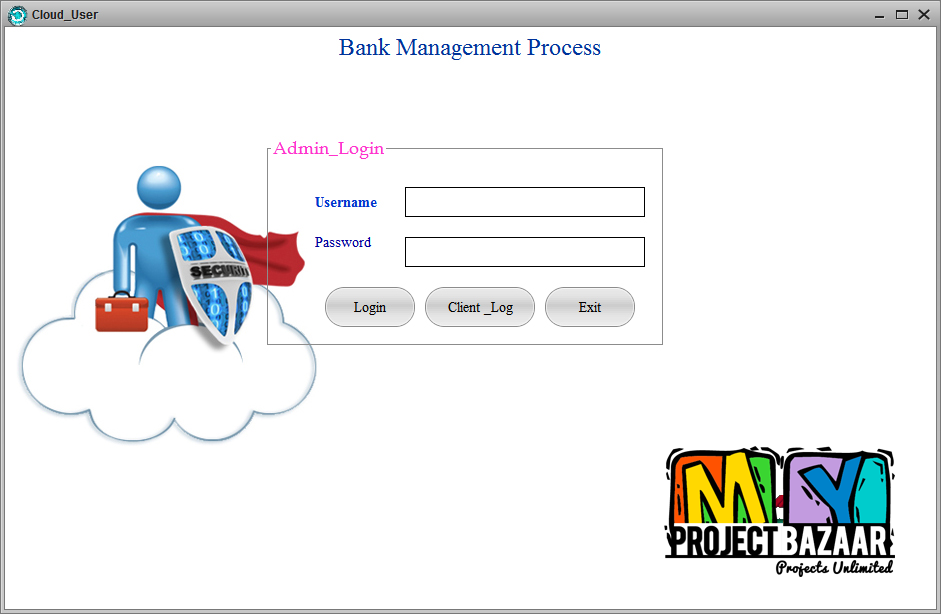
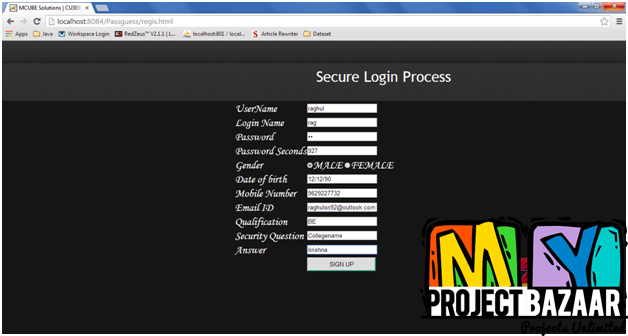
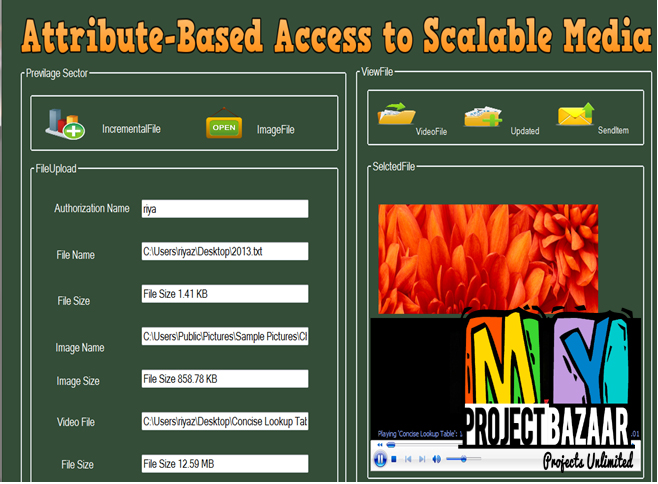
Abstract In the first place,Internet of Things (IoTs) has emerged to motivate various intelligent applications based on the data collected by various “things.”In addition, Cloud computing plays an important role for big data processing by providing data computing and processing services.In spite of,cloud service providers may invade data privacy and provide inaccurate data processing results to users, and thus cannot be fully trusted. On the other hand, limited by computation resources and capabilities, cloud users mostly cannot independently process big data and perform verification on the correctness of data processing.In a moment,special challenge on cloud computing verification, especially when user data are stored at the cloud in an encrypted form and processed for satisfying the requests raised in different contexts.even so,the current literature still lacks serious studies on this research issue.In effect,context-aware verifiable computing scheme based on full homomorphic encryption by deploying an auditing protocol to verify the correctness of the encrypted data processing result.design four optional auditing protocols to satisfy different security requirements. Their performance is evaluated and compared through performance analysis, algorithm implementation, and system simulation.As a result,effectiveness and efficiency of our designs. The pros and cons of all protocols are also analyzed and discussed based on rigorous comparison.
Including Packages
Our Specialization
Support Service
Statistical Report

satisfied customers
3,589
Freelance projects
983
sales on Site
11,021
developers
175+Additional Information
| Domains | |
|---|---|
| Programming Language |